Chasing Your Tail creator Matt notes that there are plenty of options if you want to track someone’s movements or digital activities, but few ways to identify whether it’s happening and pinpoint who’s behind it. “It’s very depressing to see how many devices are out there to spy on people, versus how many devices detecting that people are being spied on.”
Makers gonna make
Matt works for the US government with a focus on open-source intelligence, and recently gave a talk on his anti-stalking device at the Black Hat security conference. He’s not your typical security expert, though. Matt first became interested in technology aged 10 when, a year before she died, his mum bought him a TRS-80 computer as a Christmas present and he began to learn BASIC.
Computing remained a hobby when he began a career in law enforcement, but his self-taught skills came to the fore as he began reading up on how to fix and connect various office devices and equipment, “building things that needed to be built,” eventually leading to Matt being recruited as a technical agent in a government department. He credits not having a formal computing education as one of the reasons he has no fear of computers, since he’s never been aware of what boundaries there are supposed to be. Nonetheless, Matt eventually learned MySQL databases, PHP, and GIS mapping, developing a strong interest in digital forensics. A decade ago, this led to him developing and teaching an OSINT (open-source intelligence) class, including a sandbox activity simulating possible security breach risk scenarios. At this point “a light switch flipped on about the need for far more situational awareness,” he explains.
A second set of eyes
Having spent 21 years working in digital forensics for the US government, Matt is keenly aware of the dangers that covert operations bring to both handlers and those being protected. Even the most security-conscious person carries a smartphone, however, and these can easily betray someone’s location by dint of the way they’re designed to constantly look for available connections.
The challenge is not trying to give away your own location, he warns. “If I was trying to work out if someone was following me, I would go to three different places: I’d go grab a coffee, then maybe put gas in my car, then maybe go to a bookstore, and then I would look at and see, did I see any devices at all three locations?”
Years later, an attendee at that OSINT class from a different agency contacted him with concerns. “He wasn’t worried about his physical safety; he was worried about the physical safety of this person he was talking to, and meeting with,” and wanted a second set of eyes. The man was after a physical detection device to use alongside the tradecraft and surveillance detection tools he already had.
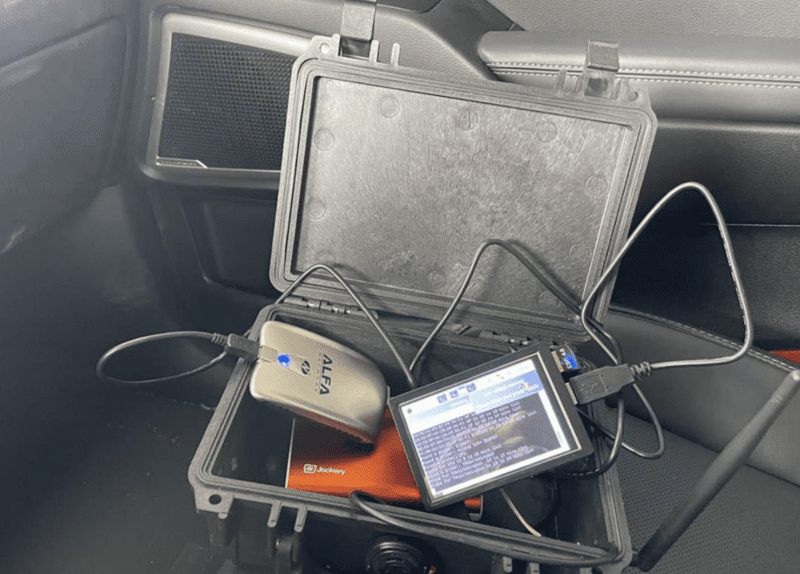
Given his history of making things, Matt already had the hardware he needed, including a pair of Raspberry Pi 3 computers, barring a cheap $25 display he bought online. “I can write ugly Python code that gets the job done usually.” A month later, Matt handed over the suitcase containing the promised anti-stalker device.
Schreibe einen Kommentar
Du musst angemeldet sein, um einen Kommentar abzugeben.